About EXECryptor
To view somethings about Execryptor visit http://www.strongbit.com/execryptor.asp
(most of these techniques are applied through the use of thread)
About Reversing
stuff detection
Execryptor uses a lot of tricks to detect ollydbg, and other tools (like softice,
filemon, regmon, etc..).This is possible, because Execryptor makes a lot of
thread , withus it does a continuous control. For example, isn't possible
uses at the same time ollydbg or filemon(not pached) with a software protected
by Execryptor.
Those problem is possible resolve with RE-pair 0.6(for regmon, filemon) and
AntidetectOllyPatch (for Olly)
About R3 degugger
detection
Execryptor uses some trick to verify if he is debugged:
- Control of Beingdebug
004XXXXX MOV EAX,DWORD PTR FS:[30] ;fs:[30] return the PEB address ... 004XXXXX ADD EAX,2 ; PEB+2 is beingdebug memory address 004XXXXX MOV EAX,DWORD PTR DS:[EAX] ; AL maybe 0(not debug) or 1(debug present) ... 004XXXXX OR AL,AL 004XXXXX JE UnPackMe.004F2C67 - Control of ProcessHeap
004XXXXX MOV EAX,DWORD PTR FS:[18] ; fs:[18] return the TEB address ... after some operation 004XXXXX MOV EAX,DWORD PTR [EAX+30] ;TEB+0x30 return the PEB address .... after some operation 004XXXXX MOV EAX, DWORD PTR[EAX+18] ;PEB+0x18 retunr the ProcessHeap address 004XXXXX CMP DWORD PTR DS:[EAX+10],0 ;EAX+10 maybe 0(not debug) or other values (debug present)
- Controll of NtGlobalFlag
004XXXXX MOV EAX,DWORD PTR FS:[30] ;fs:[30] return the PEB address 004XXXXX ADD EAX,8E4180C9 004XXXXX ADD EAX,71BE7F9F ;EAX = PEB+0X68 : address of NtGlobalFlag 004XXXXX MOV EAX,DWORD PTR DS:[EAX] ; NtGlobalFlag maybe 0x70(debug present) or 0 - Use
of Windows apis
Use CheckRemoteDebuggerPresent and IsDebuggerPresent, look msdn - Use
of Seh
With the use of many exception, Execryptor controls if there are Hardware BreakPoints004XXXXX MOV ECX,ESP 004XXXXX ADD ECX,10 004XXXXX MOV ECX,DWORD PTR DS:[ECX] ;point to Context of software 004XXXXX MOV DWORD PTR DS:[ECX],10013 ;change the context flags ... 00524C5F ADD ECX,18 ;ECX = Debug Register 7 00524C65 MOV AL,BYTE PTR DS:[ECX] 00524C67 ADD ECX,9C ;ECX = EBP register 00524C6D ADD BYTE PTR DS:[ECX],AL 00524C6F ADD ECX,4 ;ECX = EIP register 00524C75 MOV DWORD PTR DS:[ECX],UnPackMe.00522929 ;Set the eip after the seh handler .... 0052068E XOR EAX,EAX ;EAX = 0 : fixed exception 00520690 POP ECX 00520691 RETN
This is the simplest version of seh handler, beacause in other Execryptor controls also the DB register, from 0 to 3 to verify the presence of HD bp and react, therefore use memory bp. - Use
of Thread
Execryptor creates a lot of thread to control the presence of Ollydbg, modification of code like bp, etc; to elude these controls in the simpler way, we can do a code injection into CreateThread:7C81082F >MOV EDI,EDI 7C810831 PUSH EBP 7C810832 MOV EBP,ESP 7C810834 PUSH DWORD PTR SS:[EBP+1C] 7C810837 PUSH DWORD PTR SS:[EBP+18] 7C81083A PUSH DWORD PTR SS:[EBP+14] 7C81083D PUSH DWORD PTR SS:[EBP+10] 7C810840 PUSH DWORD PTR SS:[EBP+C] <-- change with JMP to_empty_space 7C810843 PUSH DWORD PTR SS:[EBP+8] 7C810846 PUSH -1 7C810848 CALL kernel32.CreateRemoteThread 7C81084D POP EBP 7C81084E RETN 18 At empty space 7CXXXXXX MOV DWORD PTR SS:[EBP+C],4 <-- Set the thread to Suspend mode 7CXXXXXX PUSH DWORD PTR SS:[EBP+C] 7CXXXXXX PUSH DWORD PTR SS:[EBP+8] 7CXXXXXX JMP kernel32.7C810846
Ollydbg can debug a software protected with Execryptor only with a path and pluings. After the patching and the installation of plugins, we can run a software, here I show how arrive at OEP and how rebuild the iat.
- Prepare
Olly to debugging
Patch olly with AntidetectOllyPatch
Open Ollydbg and set these options: Alt+O -> Exceptions ->check: Int3 , SingleStep, Memory access and add Invalid lock sequenze.
Open the option of hide debugger and check IsDebuggerPresent with Unhadled exceptions trick.
Open the option of IsDebug&Extra and check all.
- Find
the OEP
Open the menu of NtGlobalFlag and click on "Set TempBreak on Tls Callback", and "SET LDR_SHOW_SNAPS". Now open the software (in this case the crackme) and Olly will break at Tls Callback, and it sets 2 bp, delete them, and set a break-on-access on code section.
Run with alt+f9 the progie and we will break at:004F181D STOS BYTE PTR ES:[EDI] 004F181E JMP SHORT UnPackMe.004F1809
Step beyond the jmp, and find a "cmp ecx,2", because this istruction is the end of decopressing proc:004F1809 XOR EAX,EAX 004F180B CALL UnPackMe.004F1921 ... 004F18A2 MOV ECX,EAX 004F18A4 INC ECX 004F18A5 INC ECX 004F18A6 POP EAX 004F18A7 OR EAX,EAX 004F18A9 JE SHORT UnPackMe.004F18AF 004F18AB MOV EBX,EAX 004F18AD JMP SHORT UnPackMe.004F190D 004F18AF CMP ECX,2 <-- If ecx = 2 : end of decripting 004F18B2 JE SHORT UnPackMe.004F191A
Set a bp on this istruction, push alt+f9 till ecx = 2 and again 3. Now re-set the bp-on-access and remove the bp on "cmp ecx,2", push alt+f9, if there are exception push always alt+f9, and we'll break at the Oep. Here we can have stolen bytes or not, the difference is visible to eye.
No stolenWith Stolen004271B0 PUSH EBP <-- OEP 004271B1 MOV EBP,ESP 004271B3 PUSH -1 004271B5 PUSH UnPackMe.00450E60 004271BA PUSH UnPackMe.004292C8 004271BF MOV EAX,DWORD PTR FS:[0] 004271C5 PUSH EAX 004271C6 MOV DWORD PTR FS:[0],ESP 004271CD ADD ESP,-58 004271D0 PUSH EBX 004271D1 PUSH ESI 004271D2 PUSH EDI 004271D3 MOV DWORD PTR SS:[EBP-18],ESP
004271B0 JMP UnPackMe.00484321 004271B5 POP EAX 004271B6 ROL EAX,18 004271B9 JMP UnPackMe.0046C000 004271BE JO SHORT UnPackMe.004271D2 004271C0 INS BYTE PTR ES:[EDI],DX 004271C1 NOP 004271C2 XOR BL,BYTE PTR DS:[EDI] 004271C4 IN EAX,DX 004271C5 PUSH EAX <--Ipotetic OEP 004271C6 MOV DWORD PTR FS:[0],ESP 004271CD ADD ESP,-58 004271D0 PUSH EBX 004271D1 PUSH ESI 004271D2 PUSH EDI 004271D3 MOV DWORD PTR SS:[EBP-18],ESP
There're two method for find stolens:
1) Trace the loader untill the ipotetic oep
2)Use RDG for detect the compiler, analyze the stack and try to do thingsThis is the stack at Ipotetic OEP 0012FFB4 004292C8 UnPackMe.004292C8 0012FFB8 00450E60 UnPackMe.00450E60 0012FFBC FFFFFFFF 0012FFC0 0012FFF0 0012FFC4 7C816D4F RETURN to kernel32.7C816D4F <- Addr of ExitProcess
Dump the progie without rebuild the iat, and analyze this with RDG: is VC5.
Generic opcodes of entrypoint for VC5 is : "push ebp mov ebp,esp". So the value of stack addr 12ffc0 is push ebp
Now in the stack there's 0xff = -1(dec) at 12ffbc: "push -1". There are also stored two address: "push 450e60 push 4292c8". Ok now after the ipotetic OEP there's the installation of a seh handle so: "push fs:[0]".
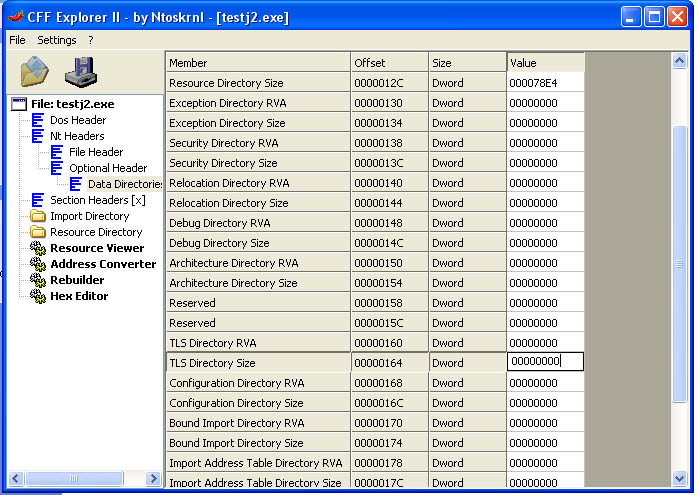
This is the rebuild code(the push eax is overwrite by push fs:[0], but the code is good because eax had the addr of fs:[0])004271B0 PUSH EBP <-- Set new origin here 004271B1 MOV EBP,ESP 004271B3 PUSH -1 004271B5 PUSH UnPackMe.00450E60 004271BA PUSH UnPackMe.004292C8 004271BF PUSH DWORD PTR FS:[0] 004271C6 MOV DWORD PTR FS:[0],ESP 004271CD ADD ESP,-58Now redump with the option of iat rebuild, open the progie with cff or another PE editor, change in Optional Header the base of code to 1000 and delete the Tls directory
Now we have a runnig progie, but the iat isn't all rebuild. To make the dump running also on other PC, you must annul the dword where there's the address of getmodulehandle in loader section in my case 487490. Dump funzionante
- Rebuild the IAT
Execryptor uses a new method to call an api, it doesn't use GetProcAddress, but:- Take an
hash
00486AA4 PUSH 2270D522 00486AA9 POP EAX .... 0048B26C ADD EAX,170A76E0 0048B272 SUB EAX,2A3E4C14 0048B278 ADD EAX,CBC09743 0048B27E SUB EAX,F5B509BF .... 0046F37C ADD EAX,80B01ADE ;EAX is the hash of api MOV right_buffer, EAX - The loader decripts
dll's name and it gets the imagebase with GetModuleHandle, it takes
the address of export table,after it generates an hash with every api
who will be compare with the right_hash, until they will be egual:
START: ;proc which generate the hash for api's name 00479416 MOV EAX,DWORD PTR SS:[EBP-C] ;ebp-c = offset name_of_Api 00479419 MOVZX EAX,BYTE PTR DS:[EAX] ;in eax there are a char TEST EAX,EAX JE END1 ... jmps ... 004851EE ADD DWORD PTR SS:[EBP-8],EAX 004851F1 MOV EAX,DWORD PTR SS:[EBP-8] 004851F4 SHL EAX,0A 004851F7 ADD DWORD PTR SS:[EBP-8],EAX 004851FA MOV EAX,DWORD PTR SS:[EBP-8] 004851FD SHR EAX,6 00485200 XOR DWORD PTR SS:[EBP-8],EAX 00485203 INC DWORD PTR SS:[EBP-C] JMP START .. ebp-8 = buffer of generate_hash.. END1: 00480044 MOV EAX,DWORD PTR SS:[EBP-8] 00480047 SHL EAX,3 .... 004714BF >ADD DWORD PTR SS:[EBP-8],EAX 004714C2 >MOV EAX,DWORD PTR SS:[EBP-8] 004714C5 >SHR EAX,0B 004714C8 >XOR DWORD PTR SS:[EBP-8],EAX ... 0048D6FE MOV EAX,DWORD PTR SS:[EBP-8] ... 004793FF SHL EAX,0F 00479402 ADD DWORD PTR SS:[EBP-8],EAX 00479405 MOV EAX,DWORD PTR SS:[EBP-8] ... CMP EAX,right_buffer JNZ NEXT_API - When the loader find the correct hash, it takes the address in memory of api and rewrite the iat_address, push the_return_addr and execute a jmp [iat_addr]
In fact this is a call before the calling:004271D6 CALL DWORD PTR DS:[460ADC] ; UnPackMe.00484466
and this is the call after the calling:004271D6 CALL DWORD PTR DS:[460ADC] ; kernel32.GetVersion
- Take an
hash